MobiSecServ 2023 - Eighth International Conference On Mobile And Secure Services, 4-5 November 2023
Papers should be submitted for publication consideration in the IEEE Xplore Digital Library
Part Number: CFP23RAC-ART
ISBN: 979-8-3503-1649-0
IEEE Conference Record #58080
Conference Venue: South Beach, Miami, Florida, USA


Full and Short Papers deadline: June 4th 2023 June 26th 2023 July 10th 2023
Full and Short Papers acceptance/rejection: August 7th 2023
Work In Progress (WIP) Papers deadline: August 28th 2023
WIP Papers acceptance/rejection: September 10th 2023
EDAS link https://edas.info/newPaper.php?c=30455
Previous Conferences
The Seventh MobiSecServ was held in February 2022 (Virtual Conference), see the conference website, and the Proceedings of the Seventh International Conference on Mobile and Secure Services
The Sixth MobiSecServ was held in February 2020 at Miami Beach, see the conference website, and the Proceedings of the Sixth International Conference on Mobile and Secure Services
The Fifth MobiSecServ was held in March 2019 at Miami Beach, see the conference website, and the Proceedings of the Fourth International Conference on Mobile and Secure Services
The fourth MobiSecServ was held in February 2018 at Miami Beach, see the conference website, and the Proceedings of the Fourth International Conference on Mobile and Secure Services
The third MobiSecServ was held in February 2017 at Miami Beach, see the conference website, and the Proceedings of the Third International Conference on Mobile and Secure Services
The second MobiSecServ was held in February 2016 at the Gainesville University, see the conference website, and the Proceedings of the Second International Conference on Mobile and Secure Services
The first MobiSecServ was held in February 2015 at the Gainesville University, see the conference website, and the Proceedings of the First International Conference on Mobile and Secure Services
A video of MobiSecServ 2015 is available at this link
An early version of MobiSecServ was organized in February 2014 at the Gainesville University, see the workshop website
A video of this previous event is available at this link
About the University of Florida and Telecom Paris
The University of Florida (UF) is a major, public, comprehensive, land-grant, research university. With more than 50,000 students, UF is now one of the largest universities in the nation. UF has a 2,000-acre campus and more than 900 buildings (including 170 with classrooms and laboratories).
Telecom Paris is an international and multidisciplinary French research centre for digital technology, which combines disciplinary expertise at the highest level and a unique capacity for a cross-disciplinary and interdisciplinary approach across all the sectoral areas in direct response to the socio-economic issues of the digital revolution. Research at Telecom ParisTech relies on 172 faculty members, 14 engineers and technicians, 70 post-PhDs, 60 visiting scientists, 285 PhD students, producing an average of 625 international publications and 20 patents. The contractual turnover is about 10.8M€.
Preliminary Program
Venue: Hilton Cabana Miami Beach
6261 Collins Avenue, Miami Beach, Florida, 33140, USA
Saturday november 4th
9h00-9h20: Welcome
9h20-9h30: Opening
9h30-10h30: keynote1, Deep Learning, Selwyn Piramuthu
Deep learning has revolutionized learning difficult concepts through mapping inputs to appropriate outputs. While deep learning is not conceptually different from what existed before this term was coined, it has some distinguishing features. We discuss the history of deep learning, its features, and associated challenges. We also briefly discuss federated learning as it relates to IoT.
Selwyn Piramuthu is Professor of Information Systems at the University of Florida, where he has taught since Fall 1991. His research interests include machine learning and cryptography with applications in financial credit scoring, IoT/RFID systems, scheduling, and supply chain management.
10h45-12h00: Session 1
10h45:
Distinguishing Sensor Faults and Attacks in Connected Vehicle Networks Using Two-Step Verification
Authors: Heena Rathore and Pranay Chowdary Jasti (Texas State University, USA); Henry Griffith (San Antonio College, USA)
11h10:
An Attack Scenario Reconstruction Approach Using Alerts Correlation and a Dynamic Attack Graph
Authors: Meaad Alrehaili and Adel Alshamrani (University of Jeddah, Saudi Arabia)
11h35:
Analysis of machine learning algorithms for DDoS attack detection in connected cars environment
Authors: Ali El Attar and Ayoub Wehby (Telecom Paris, France); Fadlallah Chbib (Telecom-Paris, France); Rida Khatoun (Telecom Paris, France); Joel Hachem (Kettering University, USA); Ahmad Fadlallah (University of Sciences and Arts in Lebanon (USAL), Lebanon); Aissaoui-Mehrez Hassane (Mines-Telecom Institute -Telecom-Paris-Institut Polytechnique de Paris, France & Laboratoire Traitement Et Communication de l'Information Paris Saclay (LTCI), France)
12h00-13h45: Lunch
13h45-16h15: Session 2
13h45:
Personalized Aging-in-Place Support through Fine-Tuning of Generative AI Models
Authors: Henry Griffith (San Antonio College, USA); Heena Rathore (Texas State University, USA)
14h10:
CNN-LSTM based Approach for DDoS Detection
Authors Tahani Ali Alasmari, Ala Eshmawi, Adel Alshamrani and Lobna Hsairi (University of Jeddah, Saudi Arabia)
14h35:
Privacy-Aware and Hardware Acceleration-Based Aggregation Scheme for Smart Grid Networks
Authors: Kayla White, Ujunwa Madububambachu and Ahmed Sherif (University of Southern Mississippi, USA); Kasem Khalil (University of Mississippi, USA); Magdy Bayoumi (University of Louisiana Lafayette, USA); Mostafa M. Fouda (Idaho State University, USA)
15h00:
Design of An Autoencoder-Based Audio Compression and Decompression System
Authors: Khaled Salah (Siemens, USA); Abdelrahman Abdelrahman (Ain Shams University, USA); Shehab Shehab Hosny (Hosny, Egypt); Sara Hisham and Doha Mustafa (Ain-Shams University, USA); Samaa Abdel Moaty and Ahmed Gamal (Ain-Shams University, Egypt); Ali Farouk (Ain-Shams Universitry, USA)
15h25:
SoftBloC: An IoT Security and Privacy Architecture for a Cashierless Retail Store
Authors: Segun Akande and Opeoluwa Tosin Eluwole (Deloitte LLP, United Kingdom (Great Britain))
15h50:
Education Application Usability Assessments: Comparison Between Blackboard and Canvas on App Reviews
Authors: Shabbab Ali Algamdi (University of North Texas, USA & Prince Sattam Bin Abdulaziz University, Saudi Arabia); Abdullah Albanyan and Stephanie Ludi (University of North Texas, USA)
16h15-16h45: Break
16h45-17h35: Session 3
16h45:
Determining the Authenticity of RFID Blocking Wallets
Authors: Katrina Arenas (Fordham University, USA); Thaier Hayajneh (Fordham Universtiy, USA)
17h10
Smart trash can with user photo capture using Internet of Things
Authors: José Varela-Aldás, Frías Paredes Diego Miguel, Jorge Luis Valle Ramos and Janio Jadan (Universidad Indoamérica, Ecuador)
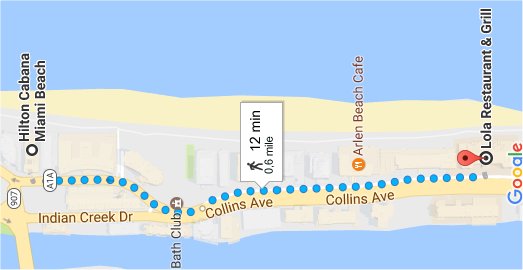
19h00: Social
Lola Restaurant & Grill, https://lolarestaurantgrills.com/
5555 Collins Ave, Miami Beach, FL 33140, USA
Sunday november 5th
9h00-9h30: Welcome
9h30-10h30: keynote2, "Internet Of Secure Elements, A New Direction For Secure Elements Use In 6G Landscape", Pascal Urien
This talk presents a new and emerging open technology named Internet of Secure Elements (IOSE), which goal is to enforce trust and security for digital platforms such as Internet of Things (IoT), blockchain, cloud computing or edge computing, thanks to on-line secure elements identified by Uniform Resource Identifiers (URIs). A Secure Element is a tamper resistant microcontroller equipped with host interfaces such as ISO7816, I2C, or SPI. Most of secure elements include a Java Virtual Machine (JVM) and execute embedded program written in the JAVACARD language. More than 10 billion secure elements are manufactured every year.
Pascal Urien is professor at Telecom Paris. His research area is computer security, more particularly based on secure elements. Applications target networks, cloud computing infrastructures, mobile applications, internet of things, blockchain systems. He is co-founders of the Ethertrust startup
10h30-10h45: Break
10h45-12h00: Session 4
10h45:
A Holistic Evaluation Model for Information Security Awareness Programs in Work Environment
Authors Talal Raji Alharbi (University of Jeddah, Saudi Arabia)
11h10:
Modelling Breach Risk in a Network of Interconnected Devices
Authors Kai E Rasmus (Luode Consulting Oy, Finland); Tero Kokkonen (JAMK University of Applied Sciences, Finland)
11h35:
Analysis of Blockchain Security: Classic attacks, Cybercrime and Penetration Testing
Authors Nour El Madhoun (ISEP Engineering School, France & Sorbonne Université, LIP6, France)
12h00-13h45: Lunch & Closing
Important Dates
Full and Short Papers submission deadline: July 10th 2023,
Full ans Short Paper acceptance/rejection: August 7th 2023
Full and Short Papers Camera ready: September 4th 2023
WIP Papers submission deadline: August 28th 2023,
WIP Paper acceptance/rejection: September 10th 2023
WIP Paper Camera ready: September 18th 2023
Scope
The goal of the "Conference on Mobile Applications, Security, and Services" is to explore the challenges, issues and opportunities for academic researchers and industrial innovators.
We are looking for both research papers on new applications and presentations of deployment experiments or new business opportunities.
This conference aims to bring researchers and industrial experts together to discuss the latest frontiers of mobile technology, and also novel applications that have not been thought of before.
In an always-on and everything connected context, mobile applications are more and more interacting with sensitive or personal resources hosted in cloud computing or Internet of Things infrastructure.
As a consequence, security and trust are critical issues, and likely a prerequisite for the deployment of IoT and Cyber Physical System and frameworks.
Digital society offers to researchers and developers a great opportunity for getting quick traction with novel applications.
The broad availability of communication technologies fertilizes research and development of novel applications and can go well beyond these intended applications.
The conference is open but not limited to the following topics:
Proximity communication technologies for mobile (NFC, Bluetooth Low Energy, ZibBee,…)
Secure transactions over proximity communications
Deployment experiments and testing for IoT Platforms
Payments, transport, ticketing, access control, couponing, macro localization (Tags)
Trust for mobile applications and services
Secure Elements, SIM frameworks; SecureSD, Single Wire Protocol (SWP)
Trusted Service Manager (TSM)
Secure over the air (OTA) services
Flash over the air (FOTA)
Hardware Secure Module (HSM)
New mobile secure architectures
Host Card Emulation (HCE)
Trusted Execution Environment (TEE)
New services and business perspectives
New payment applications
Crypto Currencies (Bitcoin, Ethereum)
Secure tokenization technologies
Proximity communication for access control
Automotive industry perspectives
Applications for the consumer industry
Applications for smart cities
Internet Of Things (IoT) new perspectives
Mobile Applications for Social Networks
Deep learning applications trust & security
